The short message service (SMS), commonly used for account verification, has become a playground for fraudulent activities, according to a study on the disposable phone number (DPN) ecosystem: “Your Code is 0000: An Analysis of the Disposable Phone Numbers Ecosystem”. Researchers from Universidad Carlos III de Madrid, IMDEA Software and IMDEA Networks have discovered significant abuse of specialized applications known as Public SMS Gateways (PSGs), which provide free DPNs, without the need to register or create an account.
The analysis, conducted over 12 months, monitored 17,141 unique DPNs in 29 PSGs, examining a dataset of more than 70 million messages. The results, which were presented at the Network Traffic Measurement and Analysis Conference (TMA) 2023, paint a troubling picture of how these DPNs, while serving as tools for user privacy protection, are exploited for fraudulent account creation and unauthorized access, particularly by circumventing security measures such as two-factor authentication (2FA).
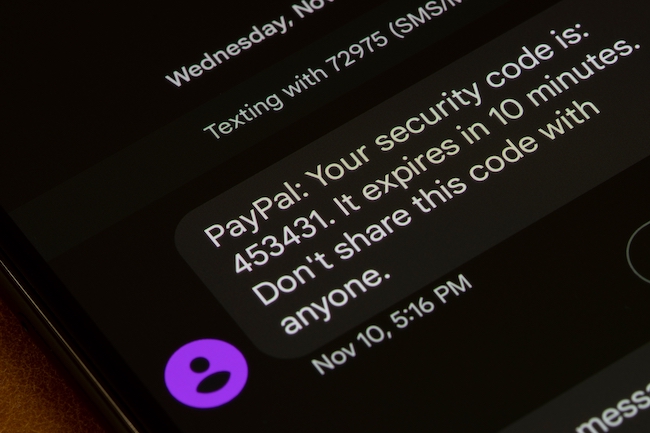
The study is the most comprehensive investigation of the PND ecosystem, and delves into the relationships between the various services that offer them. The researchers built a robust framework capable of identifying and classifying the purpose of each SMS, accurately attributing messages to more than 200 popular Internet services that rely on SMS to create registered accounts, including: Amazon, PayPal, Uber, WhatsApp, Facebook, Instagram, Google, or Tik Tok, among others.
The results highlight a global pattern of abuse affecting major Internet platforms and online services in Social Media, Entertaninment, Education and Finance. In some special cases the authors were able to link abuses to banks, telecommunication services and even public administrations. Misuse ranges from fraudulent account creation to unauthorized access, with significant impact on the security and integrity of various online platforms.
“In recent years, online services doubled down on their efforts to combat fake account creation, impersonation and unauthorized accesses. This has been achieved primary by leveraging SMS as secure channel to deliver verification messages. Our work demonstrates how the DPN ecosystem is mostly being (ab)used for circumventing these security mechanisms, without the need for a personal phone number. Compared to a previous measurement from 2018, we notice a significant increase in the usage of DPNs to create fake accounts, jumping from thousands up to millions of messages” states Srdjan Matic, researcher at IMDEA Software, one of the authors of this study.
The implications of these findings call for greater awareness and stricter security measures on the part of online service providers. As DPNs remain a popular choice for privacy-conscious users, the study underscores the urgent need to strike a balance between user privacy and protection against fraudulent activity in the changing online security landscape.